We Can Decrypt Files Locked by KeRanger Mac Ransomware, Says Russian AV Vendor
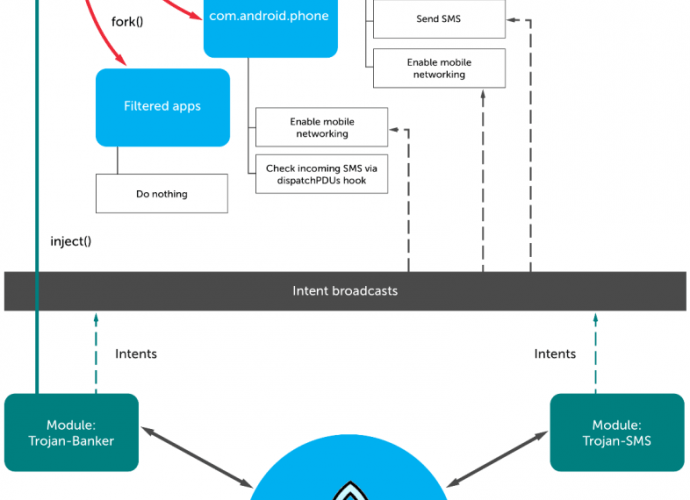
Dr.Web security researchers say they can recover files. Dr.Web, a Russian-based antivirus maker, has announced it found a method of unlocking files encrypted by the KeRanger Mac ransomware which appeared lastRead More →