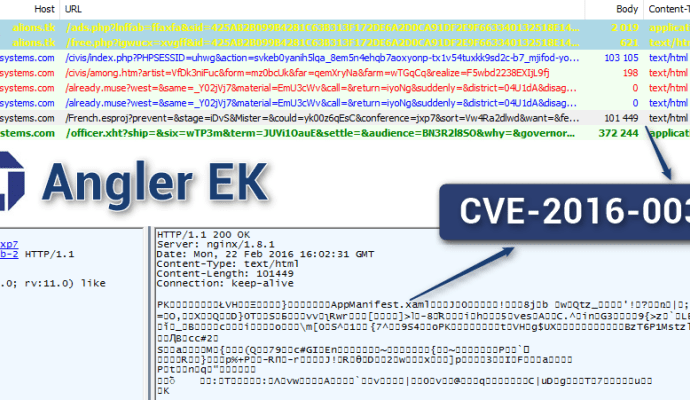
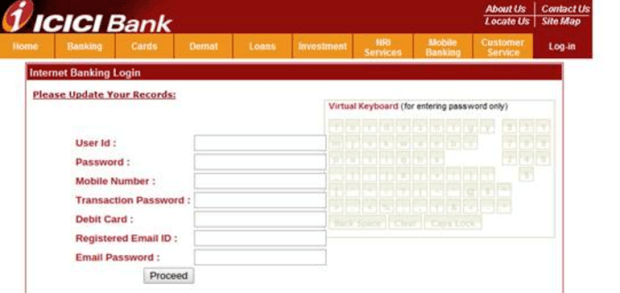
Security cameras and bank accounts can be hacked with an email as demonstrated by a hacker
All it takes to hack security cameras and bank accounts is an email, demonstrates a hacker. What happens when you challenge a series of extremely dexterous hackers to hack your bankRead More →