Almost every account password was cracked, thanks to the company’s poor security practices. Even “deleted” accounts were found in the breach. A massive data breach targeting adult dating and entertainment company Friend Finder Network has exposed more than 412 million accounts.
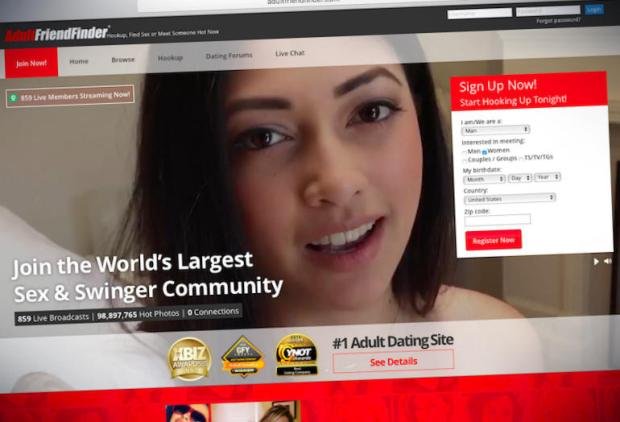
The hack includes 339 million accounts from AdultFriendFinder.com, which the company describes as the “world’s largest sex and swinger community.”
That also includes over 15 million “deleted” accounts that wasn’t purged from the databases.
 On top of that, 62 million accounts from Cams.com, and 7 million from Penthouse.com were stolen, as well as a few million from other smaller properties owned by the company.
On top of that, 62 million accounts from Cams.com, and 7 million from Penthouse.com were stolen, as well as a few million from other smaller properties owned by the company.The data accounts for two decades’ worth of data from the company’s largest sites, according to breach notification LeakedSource, which obtained the data.
The attack happened at around the same time as one security researcher, known as Revolver, disclosed a local file inclusion flaw on the AdultFriendFinder site, which if successfully exploited could allow an attacker to remotely run malicious code on the web server.
But it’s not known who carried out this most recent hack. When asked, Revolver denied he was behind the data breach, and instead blamed users of an underground Russian hacking site.
The attack on Friend Finder Networks is the second in as many years. The company, based in California and with offices in Florida, was hacked last year, exposing almost 4 million accounts, which contained sensitive information, including sexual preferences and whether a user was looking for an extramarital affair.
ZDNet obtained a portion of the databases to examine. After a thorough analysis, the data does not appear to contain sexual preference data unlike the 2015 breach, however.
The three largest site’s SQL databases included usernames, email addresses, and the date of the last visit, and passwords, which were either stored in plaintext or scrambled with the SHA-1 hash function, which by modern standards isn’t cryptographically as secure as newer algorithms.
LeakedSource said it was able to crack 99 percent of all the passwords from the databases.
The databases also included site membership data, such as if the user was a VIP member, browser information, the IP address last used to log in, and if the user had paid for items.
ZDNet verified the portion of data by contacting some of the users who were found in the breach.
One user (who we are not naming because of the sensitivity of the breach) confirmed he used the site once or twice, but said that the information they used was “fake” because the site requires users to sign up. Another confirmed user said he “wasn’t surprised” by the breach.
Another two-dozen accounts were verified by enumerating disposable email accounts with the site’s password reset function. (We have more on how we verify breaches here.)
When reached, Friend Finder Networks confirmed the site vulnerability, but would not outright confirm the breach.
“Over the past several weeks, FriendFinder has received a number of reports regarding potential security vulnerabilities from a variety of sources. Immediately upon learning this information, we took several steps to review the situation and bring in the right external partners to support our investigation,” said Diana Ballou, vice president and senior counsel, in an email on Friday.
“While a number of these claims proved to be false extortion attempts, we did identify and fix a vulnerability that was related to the ability to access source code through an injection vulnerability,” she said.
“FriendFinder takes the security of its customer information seriously and will provide further updates as our investigation continues,” she added.
When pressed on details, Ballou declined to comment further.
But why Friend Finder Networks has held onto millions of accounts belonging to Penthouse.com customers is a mystery, given that the site was sold to Penthouse Global Media in February.
“We are aware of the data hack and we are waiting on FriendFinder to give us a detailed account of the scope of the breach and their remedial actions in regard to our data,” said Kelly Holland, the site’s chief executive, in an email on Saturday.
Holland confirmed that the site “does not collect data regarding our members’ sexual preferences.”
Source:https://www.zdnet.com/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











