Siemens patched two critical vulnerabilities that affected its industrial products this week. One, tied to a recently disclosed flaw in Active Management Technology – a function of certain Intel processors – could have allowed an attacker to gain system privileges. Another vulnerability could have let an attacker upload and execute arbitrary code.
The Department of Homeland Security’s Industrial Control Systems Cyber Emergency Response Team (ICS-CERT) warned about both vulnerabilities on Thursday.
Each issue received a CVSS v3 rating of 9.8, something that indicates the vulnerabilities are critical in nature.
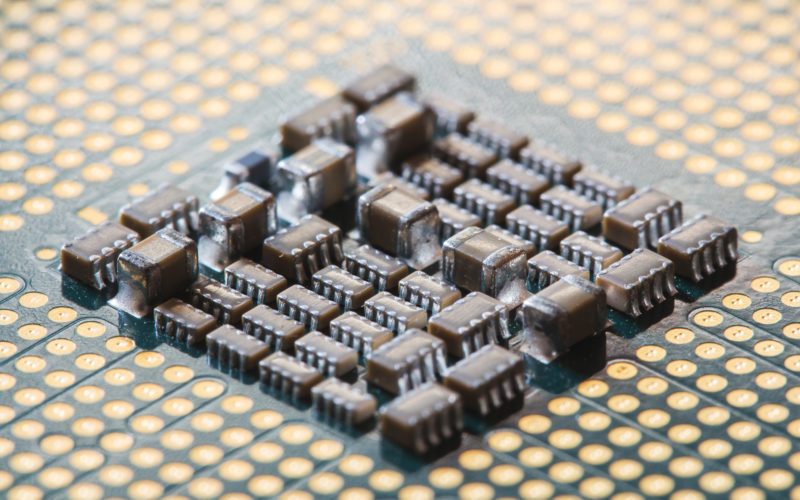
The first vulnerability stems from several Intel chipsets – Intel Core i5, Intel Core i7, and Intel XEON – that figure into Siemens products. Equipment commonly found in chemical, energy, and water/wastewater facilities, such as the company’s SIMATIC industrial PCS, SINUMERIK Panel Control Unit, and SIMOTION P320 PC all use the chips. Siemens warned Thursday that chips that have the AMT function enabled could open products up to remote code execution.
According to a security advisory from Siemens an attacker could exploit the vulnerability to gain system privileges to provisioned Intel manageability SKUs, like “Intel Active Management Technology (AMT), Intel Standard Manageability (ISM) and Intel Small Business Technology (SBT).”
ICS-CERT and Siemens’ warning comes almost two months after researchers with Embedi first disclosed the AMT vulnerability (CVE-2017-5689). The Berkeley, Calif.-based firm said at the time it was likely the vulnerability, which can easily let an attacker bypass authentication, was a programmer’s mistake. Attackers in Southeast Asia known as Platinum became the first APT group found abusing the feature earlier this month. Microsoft said the attackers were using a file-transfer tool to take advantage of AMT and run malicious code on targeted machines.
The company pushed updates for most of the SIMATIC IPCs earlier this week but says it’s still working on developing fixes for affected SINUMERIK PCUs.
A full list of affected products and patches can be found at the company’s support portal.
The second vulnerability affects the company’s ViewPort for Web Office Portal. In versions prior to revision number 1453 Siemens said an attacker could send specially crafted network packets to port 443/TCP or port 80/TCP. By doing so an attacker could have the potential to upload and execute arbitrary code. If carried out successfully the code would have the permissions of the operating system user.
The Web Office Portal lets users retrieve data from control centers. The portal is commonly found in energy company setups.
ICS-CERT also warned of equally critical but unpatched vulnerabilities in Schneider-Electric’s U.motion Builder this week. The product is a web-server-based system for automation networks, usually found in commercial, critical manufacturing, and energy facilities.
A handful of issues, including a SQL injection vulnerability, a path traversal vulnerability, denial of service, and improper access control vulnerability, plague versions 1.2.1 and earlier, ICS-CERT warns.
The most pressing issue, the SQL injection, could let an attacker perform arbitrary SQL statements against the underlying database. The software also comes with a hard-coded password for its system web access account and includes a hard-coded valid session, something which could allow an attacker to bypass authentication.
Schneider-Electric warned of the vulnerabilities on Tuesday but said it doesn’t plan to issue a firmware update to resolve them until the end of August.
“When available, it is highly recommended that U.motion Builder users apply the patch in a timely manner,” a security notification (.PDF) posted to the company’s site reads.
In the meantime the company is urging users to minimize network exposure, isolate networks behind firewalls, and only access systems remotely via VPN.

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.