A few years ago ebooks began to being sold massively, requiring companies participating in this industry (Amazon, Adobe, Barnes & Noble, among others) to invest considerable efforts to protect their intellectual property from piracy and illegal distribution on the Internet.
In this article, cyber security experts from the International Institute of Cyber Security (IICS) will show you what these protection mechanisms consist of and what methods hacking groups use to breach and access this information by illegitimate means.
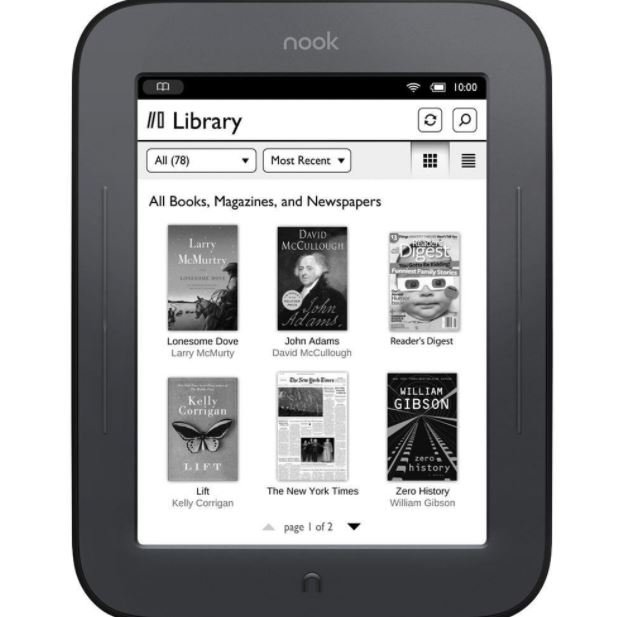
Before we begin, it is worth remembering the rise in popularity of the ebook, which is considered by many to be a more environmentally friendly alternative than the traditional book industry. Its popularity increased on par with the massive use of smartphones and electronic tablets and even devices such as the Kindle to the point where ebook sales outweighed sales of physical books on platforms like Amazon.
Unfortunately nothing lasts forever, so by the end of 2016 there had been a critical slowdown in sales in this industry. A few years later the picture looks more complicated even for the production of an ebook, whose costs are already equated or exceed the production costs of a traditional book, and that security restrictions on an ebook have limited the growth of its popularity, as many people consider it useless to buy a protected file that cannot be borrowed, sold or donated after a while.
IICS cybersecurity specialists mention that Digital Rights Management (DRM) refers to the security mechanisms that copyright holders implement to protect any digital development, including ebooks. In this case, encryption is the most commonly used option, although there are multiple methods to prevent piracy.
Let us take a brief look at this industry which, while facing a severe crisis, refuses to change the logic of its work in favor of options more convenient for all.
PDF: The industry’s favorite format
Adobe PDF Reader was one of the first formats to have DRM protection. The protection of this format seemed to live up to expectations until developer Dmitry Sklyarov found a way to hack this protection, leading him to a jail in the U.S. Although at the time the authorities of multiple countries appeared to have undertaken strict surveillance against the attempted DRM hacking, this practice became increasingly common and it is even possible to discuss this issue in conventional Internet forums.
Adobe PDF Merchant (Acrobat Web Buy)
Although Adobe PDF Merchant is now of exclusively historical interest, this is the format that allows you to understand what DRM protection is when applied to electronic publications. The basic principles of DRM protection have changed little since then, although implementation has undergone substantial changes.
Support for ebooks appeared as a downloadable module in Acrobat Reader 4.05 and the first module of its kind was Acrobat Web Buy. The module’s work was based on close interaction between the client device and the server. When a user tried to open a protected workbook, this module sent the DRM server a request that contained an identifier for the environment where it was about opening this protected workbook (hard drive serial number, user account ID, etc.). This is how these protection mechanisms operate today.
The server was responsible for verifying the legitimacy of access to the protected document. If verification was successful, an RMF format such as XML was sent to the user’s system; this file contained the key to decrypt the PDF, plus a list of allowed actions and a certificate to validate the license.
In turn, the license was verified by two 1024-bit RSA keys; one belonged to the publisher and the other was used by Adobe as a trusted certificate to sign the publisher’s public key. This security mechanism was built in such a way that it was impossible to create a secure RMF file (and therefore a secure eBook) without Adobe’s involvement. On the other hand, if hacking groups could get an RMF file, it was easy to extract their encryption key.
Adobe DRM (EBX)
This is one of the latest adobe deployments, which worked in conjunction with EBX Workgroup. This DRM system is based on generating two asymmetric keys when you start an application to read ebooks; the public key is registered on the server and the secret is sent to the user’s device. When purchasing the license, the user receives an XML file that contains the document password; the key is encrypted with the user’s public key, as well as containing a list of access rights to validate user information.
Although reliable, this mechanism is considered imperfect. Not to mention that no significant improvements have been made since its early releases, so anyone with cybersecurity knowledge could compromise this information.
DRM PDF Vulnerabilities
It is incredibly difficult to implement these mechanisms to books in PDF format and not functional in real-world scenarios. One of the main problems is that the entire schema would be exposed just by intercepting the encryption key.
With this in mind, Acrobat Reader 6 implemented a new scheme that gave security modules the ability to decide how a particular fragment of a PDF document was encrypted. Key interception stopped working because the key is no longer transmitted between the protection nodes. This still brought new problems, along with the adoption of Adobe Acrobat Reader as a standard ebook reader.
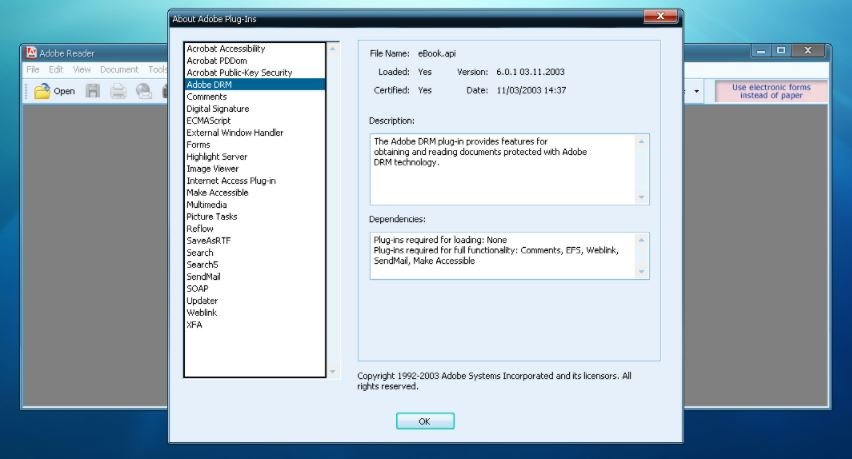
Acrobat Reader began implementing plugin support. Many researchers and even some hackers working in the piracy market discovered that, if you load a specially designed plugin at the time you open a protected PDF, it is possible to obtain the complete information of that file.
Since then this scenario has been transformed into a cat-and-mouse game, with Adobe releasing frequent improvements to prevent these attacks and hackers adapting to what the company has, abusing the possibility of loading malicious plugins with fake digital signatures, a problem that continues to affect the company.
DRM and Amazon
Amazon is the largest ebook store and even has its own ecosystem to access its content, including Kindle family products and Fire tablets. Amazon readers are also limited by a fundamental issue: this product family does not support DRM-free ebooks formats, such as ePub or FB2.
Kindle books support DRM; the link goes to the user’s Amazon account. In Kindle for iOS apps, books are encrypted exclusively with a key generated from the user’s account information. The important thing here is that it is quite difficult to extract information from an iPhone or iPad, mentioned by IICS cybersecurity experts.
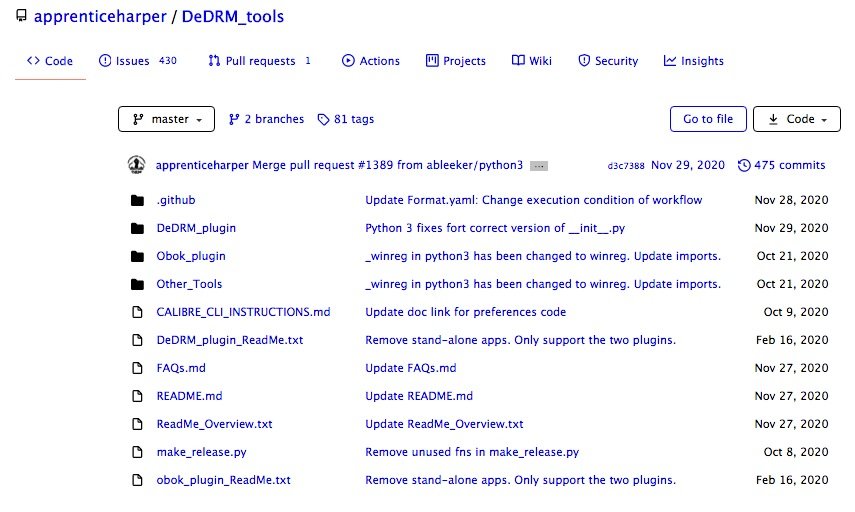
For the Kindle family, protection is based on the device’s serial number and the unique PID that is assigned during registration. As a result, the key to decrypting books downloaded to those devices can be calculated based on your Kindle’s serial number and PID. The latter can be extracted using the DeDRM Tools tool, running the following script and passing the device serial number as a parameter (the Kindle device itself must be connected to the computer at this time):
$ kindlepid.py <Kindle Serial Number>
The Windows application also uses shared key encryption per account. However, retrieving books from a Windows computer is much easier than on an Apple system, so Amazon uses a second layer of encryption, this time with a unique separate session key for each book.
Although this is a prominent mechanism, both keys are still stored on the computer and recovering them is an almost trivial issue, cybersecurity specialists say.
Here’s how to evade DRM protections for Kindle formats:
- Install the Kindle Reader for Windows app on your computer
- Download the DeDRM tool (available on GitHub)
- Install Caliber
- Install the plugin DeDRM_plugin.zip in Caliber from DeDRM_calibre_plugin
- You can now download books with the Kindle app
- The rest is simple: drag and drop books in AZW3 or MOBI formats from the Documents-My Kindle Content folder in Calibre. The DRM mechanism will be automatically removed
- Books can be converted to FB2, ePub or any other Caliber-compatible format
Optionally, you can do without Calibre using a command-line utility or simply resort to one of the many online services.
In response to the multiple methods of dodging its security mechanisms, in 2015 Amazon released KFX, a more advanced format and with greater DRM security that to date has not been decrypted by researchers or hacking enthusiasts. To the company’s bad fortune, the use of this format never became widespread, resulting in a very limited number of titles available on KFX.
Barnes & Noble: Adobe Digital Editions Protection (ADEPT)
Barnes & Noble is the second largest library chain in the U.S. and uses the ePub format, protected by the Adobe Digital Editions (ADEPT) schema. This scheme uses an encryption system that has not yet managed to become a reliable DRM scheme. According to cybersecurity experts, each book is encrypted with a unique AES key, and the key itself is encrypted with an RSA key, which is generated based on the user’s credentials (information based on an email address) and stored on the user’s computer.
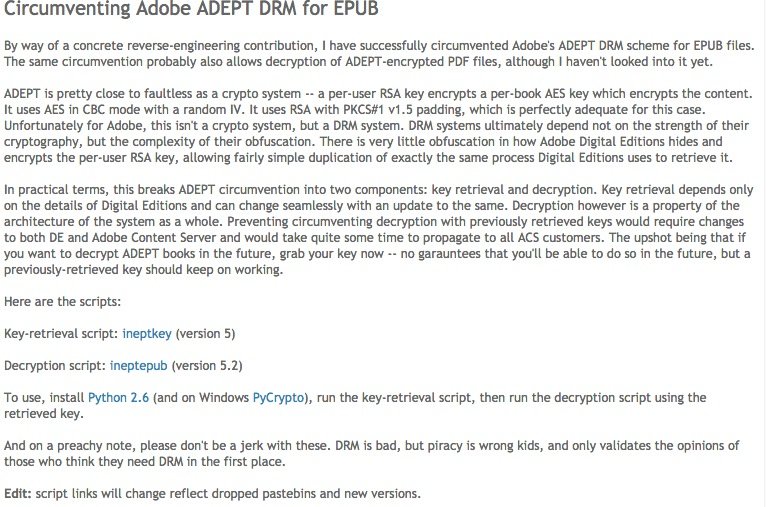
Barnes & Noble is the second largest library chain in the U.S. and uses the ePub format, protected by the Adobe Digital Editions (ADEPT) schema. This scheme uses an encryption system that has not yet managed to become a reliable DRM scheme. According to cybersecurity experts, each book is encrypted with a unique AES key, and the key itself is encrypted with an RSA key, which is generated based on the user’s credentials (information based on an email address) and stored on the user’s computer.
Hackers need to find the session key with which the RSA key was protected, which was used to encrypt the AES key used to encrypt the books. It sounds complicated, but according to the hacker who managed to break this protection, deploying the entire chain was more tedious than difficult.
Even less DRM
By now not all ebook publishers pay much interest to DRM mechanisms, even some publishers in Germany and England have concluded that these protections are detrimental to sales, leaving behind their use and opting for what they called social DRM.
Although publishers do not want to leave Amazon (it remains their most exposed platform), many also resort to selling their titles on their own websites or on third-party platforms, with the particularity that these versions of their books do not have DRM, a practice that has resulted from the liking of a considerable number of readers who prefer digital formats over the physical book.
As mentioned above, some publishers opt for the social DRM option, which allow them to reliably track the origin of books purchased in the public domain thanks to a watermark invisible to the user. In the most extreme cases, publishers simply rely on the word of honor of users, eliminating any kind of protection.
The present and future of the ebook
Given the current conditions, cybersecurity specialists consider that ebook stores that do not have their own ecosystem see their options limited to two possible scenarios: offering free downloads in widespread use formats, or selling access to their websites as a kind of streaming platform.
The second option doesn’t sound crazy in the first instance, but it leads to severe problems for users who invest their money on these platforms. For example, in the catalog offered by Liters users will frequently find all kinds of warnings such as those shown below:
THE BOOK WAS PURCHASED IN THE ONLINE STORE WWW.FEISOVET.RU
BUYER: Oleg Afonin (aoleg@voicecallcentral.com) ORDER: 287253385/09-Mar-2018
COPYING AND DISTRIBUTING THE TEXT OF THIS BOOK FOR ANY PURPOSE IS PROHIBITED!
That’s not all. In addition to this irritating announcement, this platform also places some bookmarks in its texts, such as:
#287253385 / 09-мар-2018
This is an anomaly that social DRM drivers were unable to foresee, which is unfortunate considering that there are users who invest their money on these platforms and never expect to encounter such failures.
Conclusions
DRM protection methods generally work for the vast majority of conventional users (which, in fact, is their primary goal). However, it is obvious that any user with sufficient knowledge could dodge these limitations, as this is not even too difficult. At the same time, the only major player in this industry that invests its resources to counter this practice is Adobe, as it seems that the rest of the companies have given this battle for loss.
The other side of the coin (social DRM) also does not seem to turn out as intended, consider cybersecurity experts. This practice still faces more questions than certainties, so DRM-free ebook users will still not enjoy a fully satisfying experience.
Time keeps going and the industry remains in crisis, so the complete demise of the traditional book industry, one of the most adventurous predictions during the ebook boom, is also far from realized.

Cyber Security Specialist with 18+ years of industry experience . Worked on the projects with AT&T, Citrix, Google, Conexant, IPolicy Networks (Tech Mahindra) and HFCL. Constantly keeping world update on the happening in Cyber Security Area.











