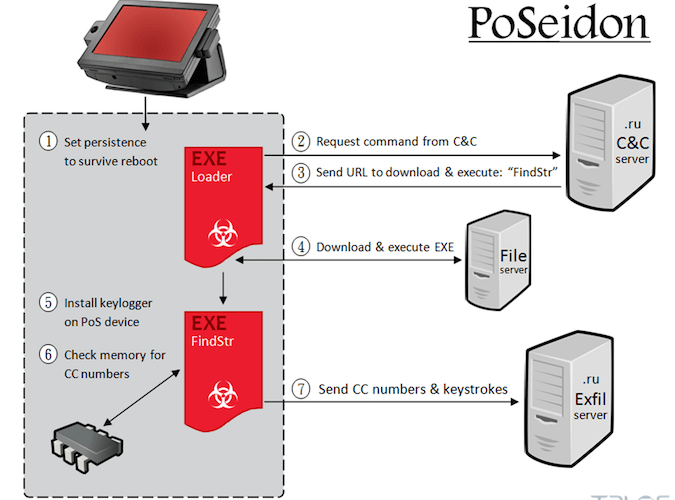
New PoS Malware LockPoS emerges in the threat landscape
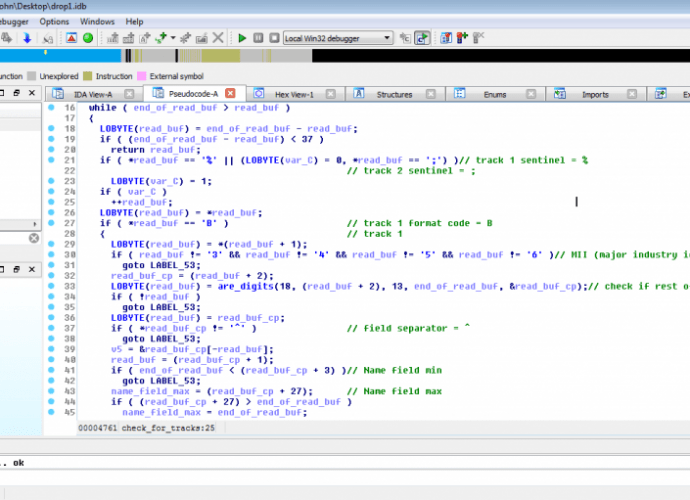
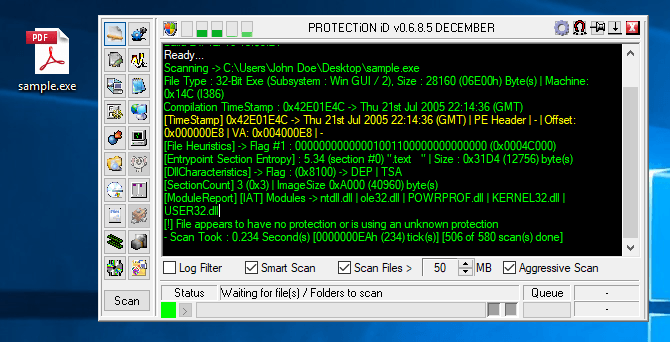
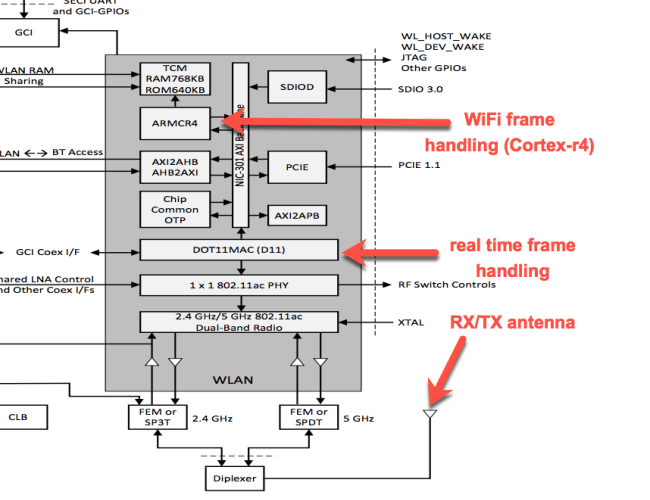
A newly discovered Point of Sale (PoS) malware dubbed LockPoS appeared in the wild and it is being delivered through the Flokibot botnet. A newly discovered Point of Sale (PoS) malwareRead More →