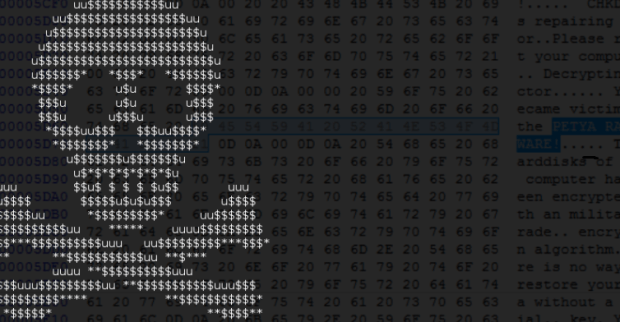
Cyber insurance shopper checklist: Things to consider before hiring these services
Information security related incidents have become so common that any organization, whether it is a major multinational company or a small business, must consider any possible protective measures against disastrousRead More →