A giant botnet behind one million malware attacks a month just got shut down
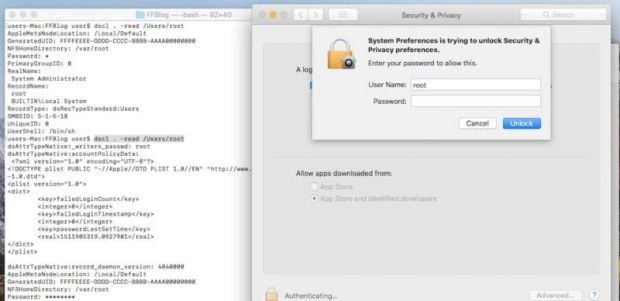
An arrest has been made over the Andromeda botnet, following an operation involving the FBI, Europol, and cybersecurity companies. A major botnet, which incorporated millions of PCs and is associatedRead More →