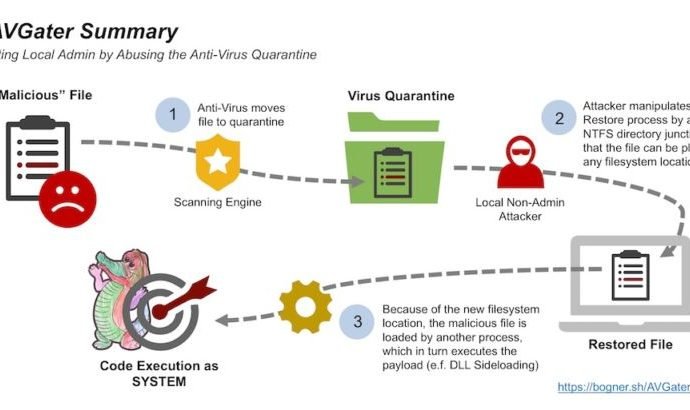
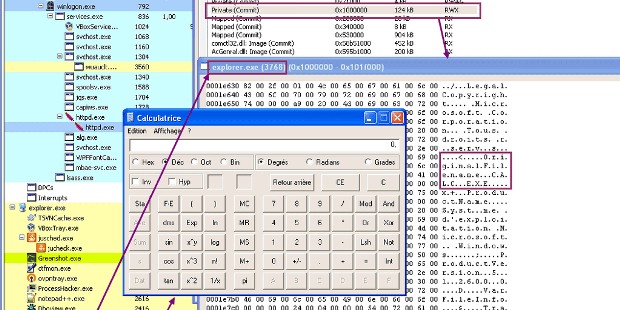
Antivirus Software Can Be Hijacked to Compromise Windows Systems
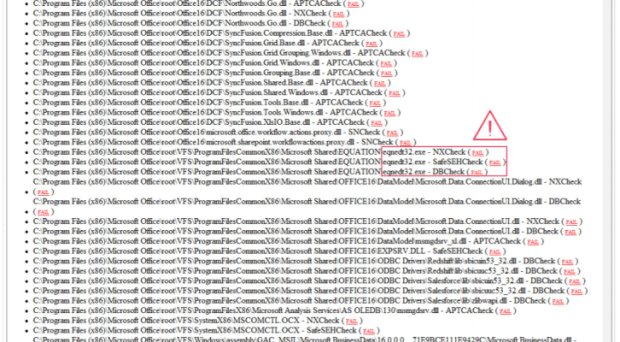
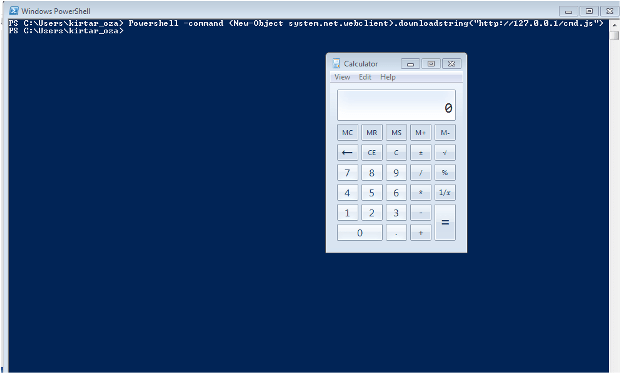
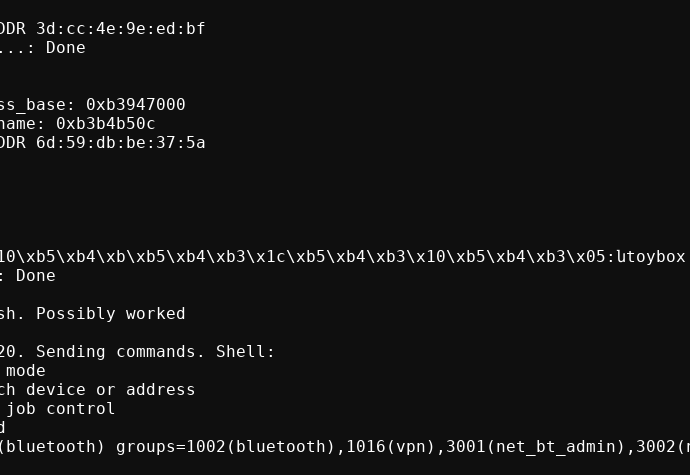
Vulnerability allows to abuse option to restore files from quarantine and then deploy malware in sensitive location. Despite Microsoft making Windows Defender a more advanced security product, third-party antivirus solutionsRead More →