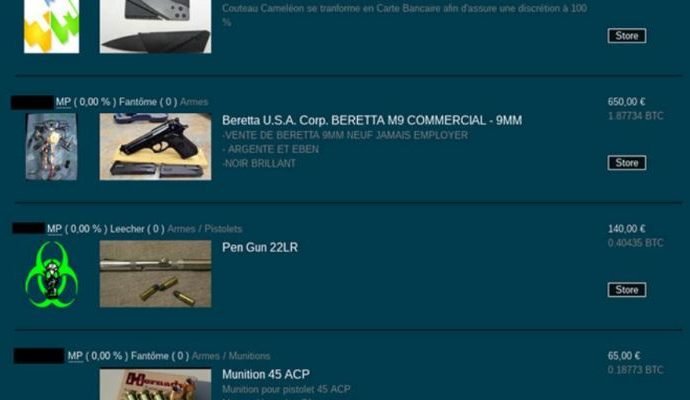
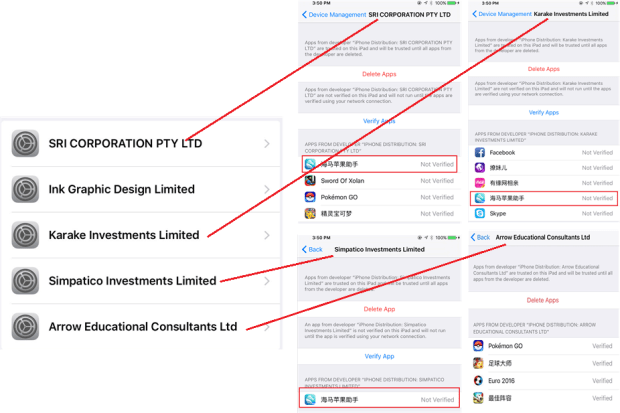
Boffins analyzed EXIF metadata in photos on principal blackmarkets
Two researchers have analyzed images Exif metadata included in the photos used by crooks to advertise their products on black marketplaces in the dark web. Darknets are a privileged environmentRead More →