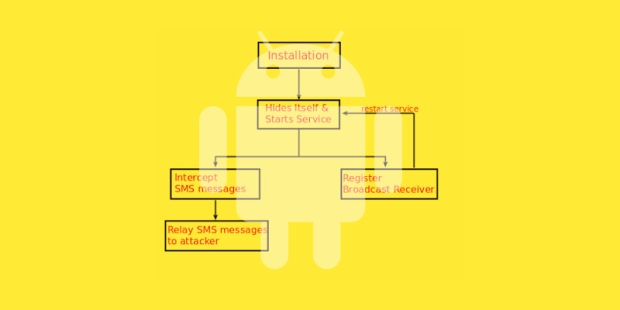
Mazar BOT Android Malware Can Erase Your Phone’s Data, Except If You’re Russian
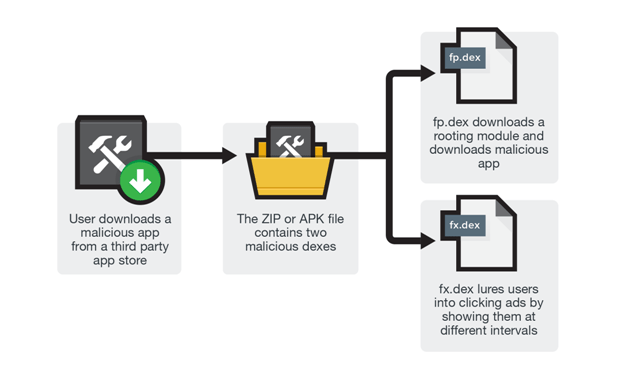
Mazar BOT is spread around via SMS/MMS spam. A new Android malware variant has surfaced that has rooting capabilities, can wipe your phone’s storage, and has many other hidden capabilities thatRead More →