Dell Adds Boot Scanner to Protect Users Against Bootkit Malware
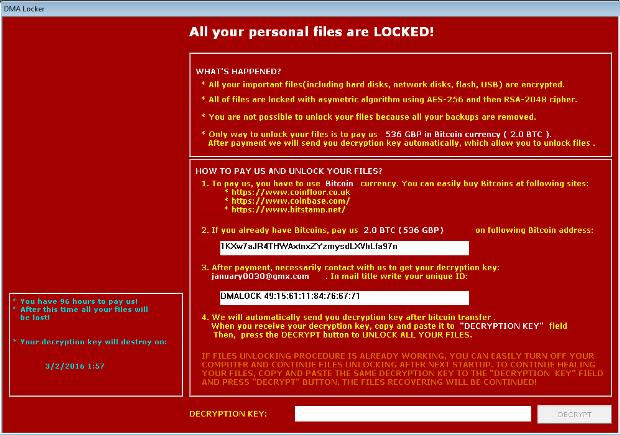
Dell and Cylance join the fight against bootkits. Dell has announced a partnership with Cylance, which will add a new security layer for its line of motherboards, a BIOS integrity verificationRead More →