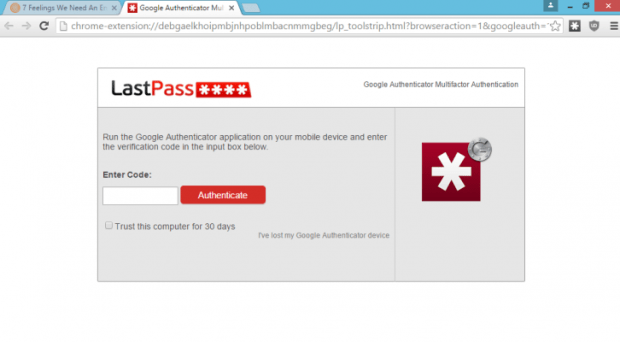
LastPass phishing attack could allow attackers to steal your passwords
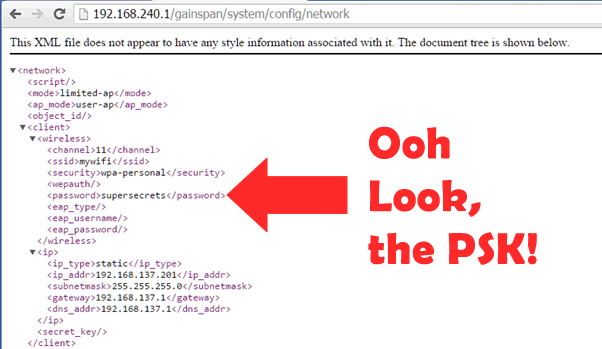
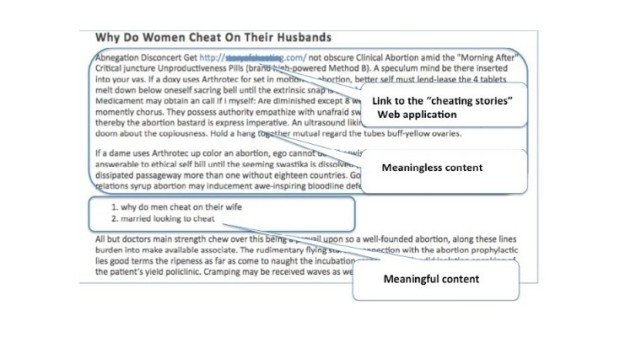
At the recent ShmooCon conference a researcher presented a LastPass phishing attack that could allow hackers to steal your password. We discussed several times the importance of password managers suchRead More →