Advantech ICS Gear Still Vulnerable to Shellshock, Heartbleed
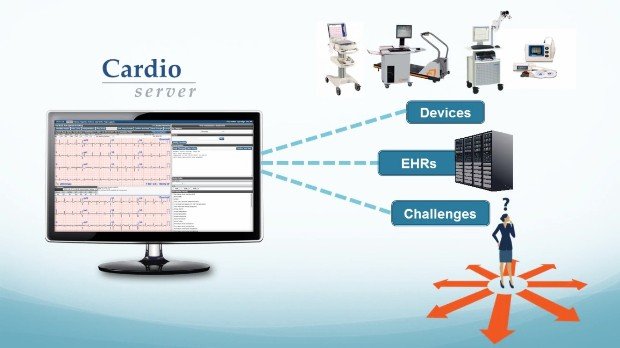
Twice in the past year, security researchers have found and reported critical vulnerabilities in Modbus gateways built by Advantech that are used to connect serial devices in industrial control environmentsRead More →