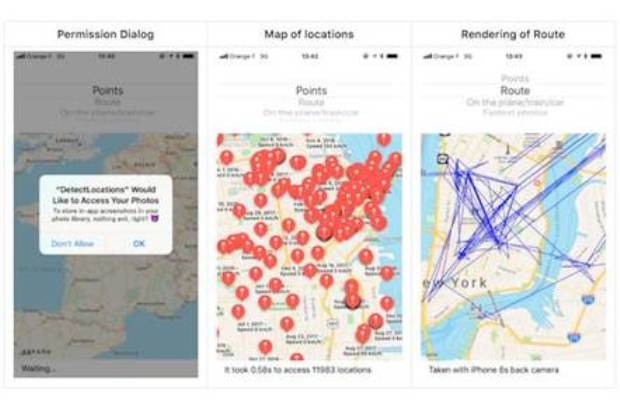
Biggest taxi firm in Russia hacked to order all the cabs to same place at once. Causing huge traffic jam like in James Bond movie
Unlike what happens worldwide, Google is not the first search engine in Russia, but a giant that brings together different services and is known as Yandex. To its credit, thereRead More →