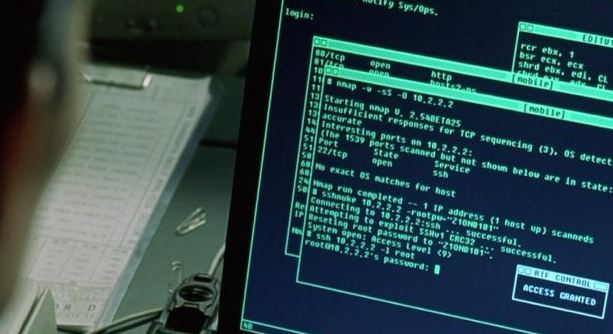
Three critical vulnerabilities in AXIS CCTV cameras allow hackers to spy on you. Patch immediately
A security firm reported the discovery of three vulnerabilities in the software of CCTV devices of technology firm Axis Communications, which has already acknowledged the flaws and issued the correspondingRead More →