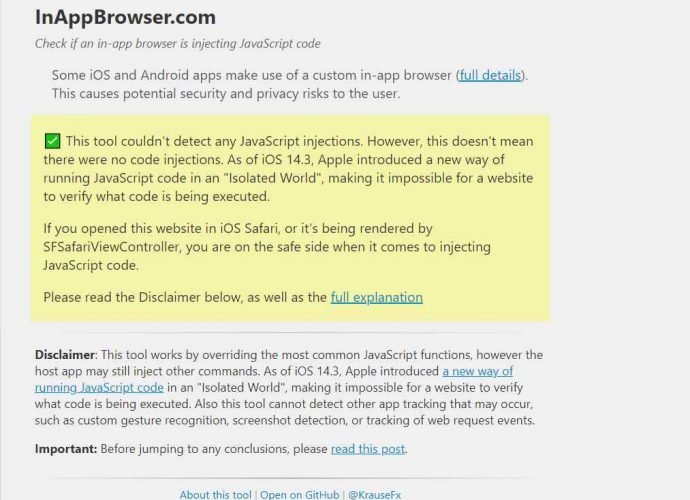
This free tool easily lets you find if JavaScript code is being used in browser inside apps to track your activity
A researcher has created a free and open source tool that anybody can use to inspect what code is being injected by such browsers. The researcher did a study toRead More →