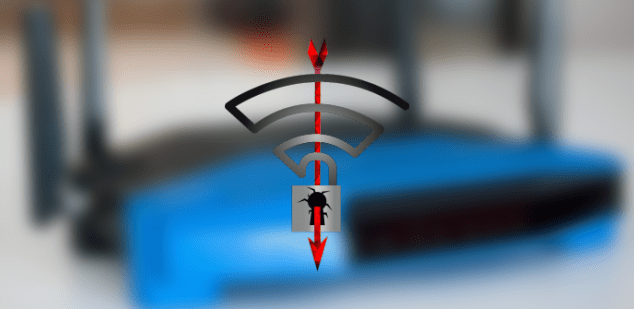
How Lynx Ransomware Extorts Millions from U.S. Companies
First discovered on July 17, 2024, Lynx ransomware quickly made a name for itself by targeting high-profile U.S. companies and extorting millions in ransom payments. Built on the remnants ofRead More →