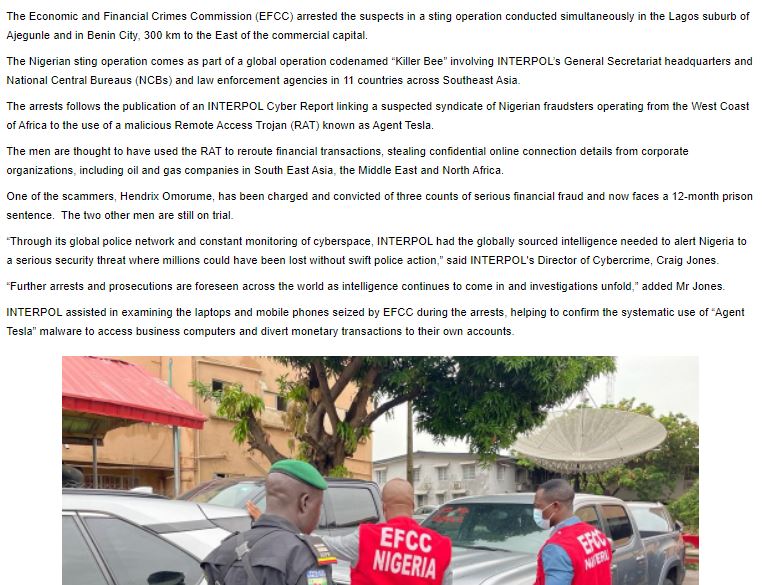
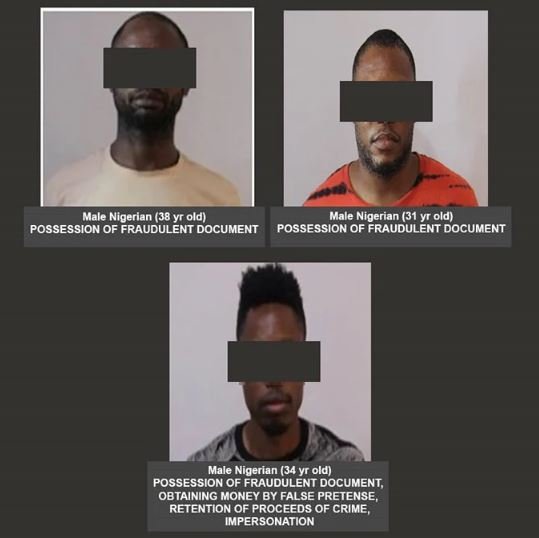
Interpol announced that Operation Killer Bee, deployed in collaboration with authorities in 11 countries in South Asia, led to the arrest of three Nigerian nationals accused of using a remote access Trojan (RAT) to divert funds and steal access credentials from affected organizations. This cybercriminal group operated from Lagos, Nigeria, and reportedly attacked multiple oil and gas companies in the Middle East, North Africa, and Southeast Asia, stealing an undetermined amount.
One of those arrested faces charges of possession of fraudulent documents, impersonation, and obtaining money with false claims, and could spend more than three years in prison. The other two defendants face only one count of possession of fraudulent documents, which Interpol believes they would have used in a business email compromise (BEC) campaign.
During the arrest of the three individuals, laptops and smartphones used for this fraudulent operation were confiscated, allowing law enforcement to discover that the hackers were using the RAT known as Agent Tesla. This malware variant allows information theft, keystroke logging, and theft of credentials stored in web browsers, email clients, and other platforms.
The defendants allegedly used Agent Tesla to steal credentials in the targeted organizations, in addition to accessing internal emails and maintaining constant surveillance of employees in these companies. The collection of information about the target is a fundamental part of a BEC attack since threat actors need to know the processes, standards, and actors involved in the processes of the affected organizations.
Cybersecurity specialists report that Agent Tesla has become one of the most widely used malware variants today, above other variants such as AveMaria, Formbook, Lokibot, RedLine, and Wakbot.
In recent days, Interpol also collaborated with the arrest of the alleged leader of SilverTerrier, another BEC operation allegedly run by cyber criminals in Nigeria.
Feel free to access the International Institute of Cyber Security (IICS) websites to learn more about information security risks, malware variants, vulnerabilities, and information technologies.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











