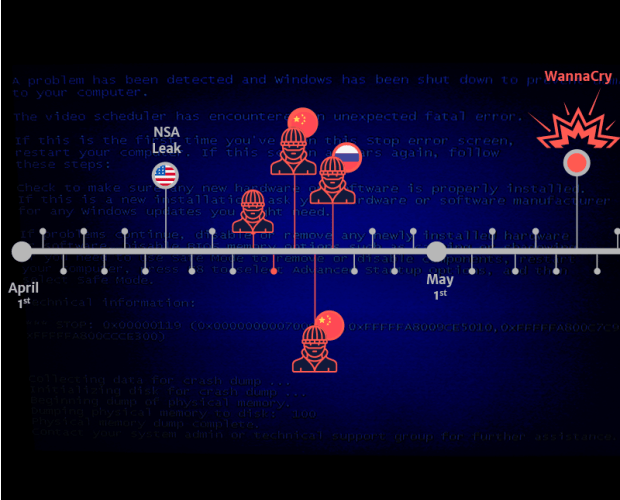
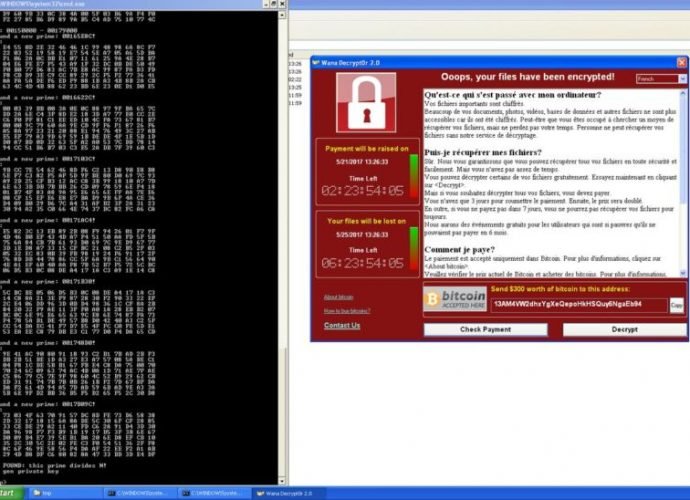
More people infected by recent WCry worm can unlock PCs without paying ransom
A tool released on Friday decrypts PCs running a fuller suite of Windows versions. New hope glimmered on Friday for people hit by last week’s virulent ransomware worm after researchersRead More →