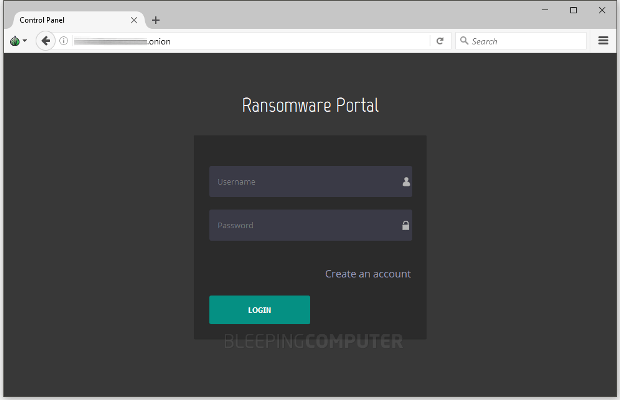
News Brief: BitKangoroo Ransomware Deletes Your Files If You Do not Pay
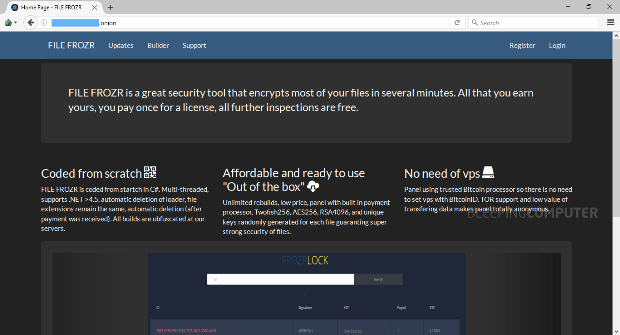
I am trying something new where I will post in brief articles about new ransomware as they are released. Many of these ransomware infections do not warrant a full article, butRead More →