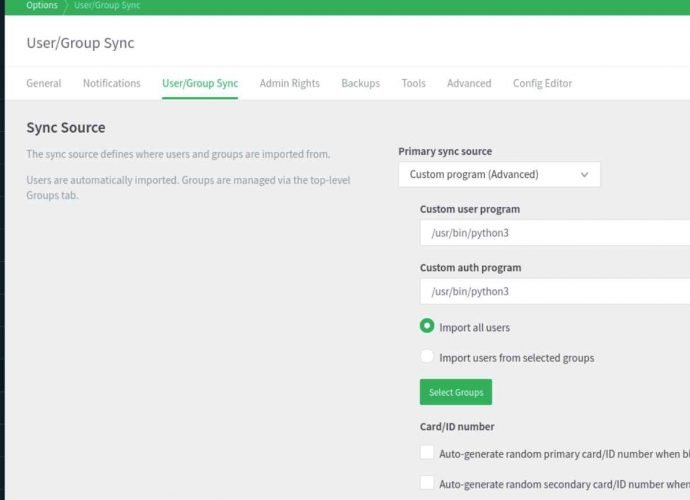
How to detect most advance Russian FSB malware “Snake” in your network
The Federal Bureau of Investigation (FBI) made the announcement on Tuesday that it had successfully disabled a network of compromised computers that Russian agents had been using for years toRead More →