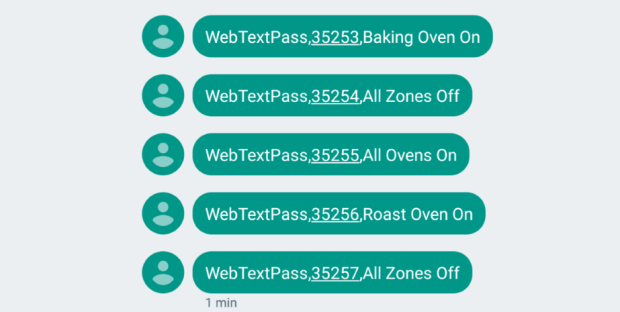
Linux remote root bug menace: Make sure your servers, PCs, gizmos, Android kit are patched
Ping of pwn: Malicious UDP packets may take over gear. A Linux kernel flaw that potentially allows miscreants to remotely control vulnerable servers, desktops, IoT gear, Android handhelds, and more,Read More →