RTM: Stealthy group targeting remote banking system
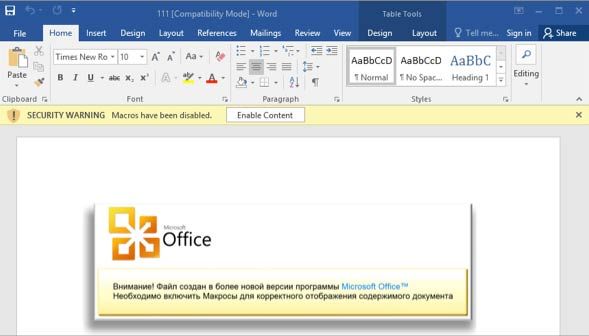
Today, we have released a white paper on RTM, a cybercrime group that has been relentlessly targeting businesses in Russia and neighboring countries using small, targeted campaigns. This group, activeRead More →