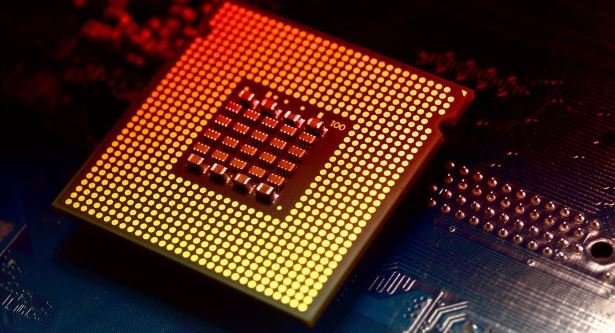
The video game Watch Dogs: Legion is hacked. 558 GB of source code available for free download
A hacking group just leaked the source code of Watch Dogs: Legion, one of the most popular video games of its kind. There are still no clear reports on whatRead More →