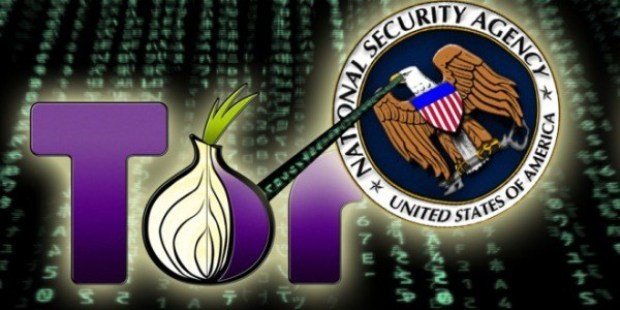
Tor veteran Lucky Green exits, torpedos critical ‘Tonga’ node and relays
Chap responsible for very early nodes says ‘recent events’ make it impossible to continue. Tor’s annus horribilus continues, with one of its earliest contributors, Lucky Green, quitting and closing downRead More →