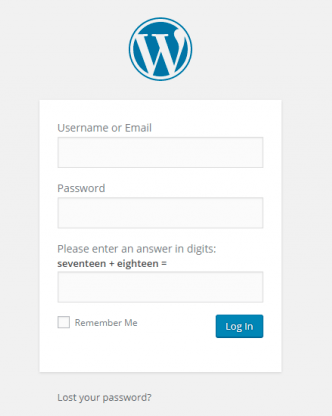
Scan any URL for XSS (cross site scripting) vulnerability
In recent years, XSS attack was found in many web applications, including microsoft, facebook, many more. XSS allows attacker to run malicious scripts. XSS (Cross site scripting) happens because ofRead More →