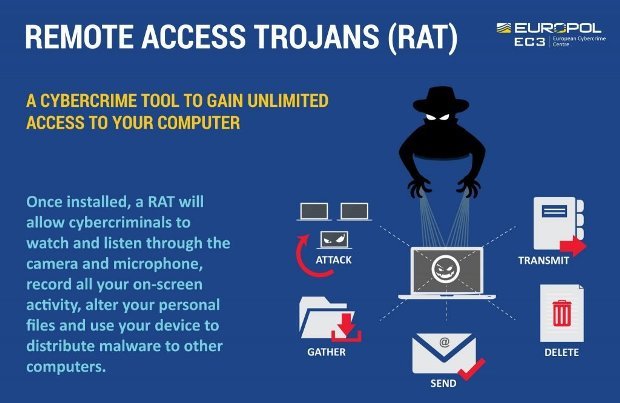
UK-led police operation quashes Luminosity Link RAT
A hacking tool that was able to give full remote control of a victim’s computer to anyone with nefarious intentions has been taken down in an international law-enforcement operation, according toRead More →