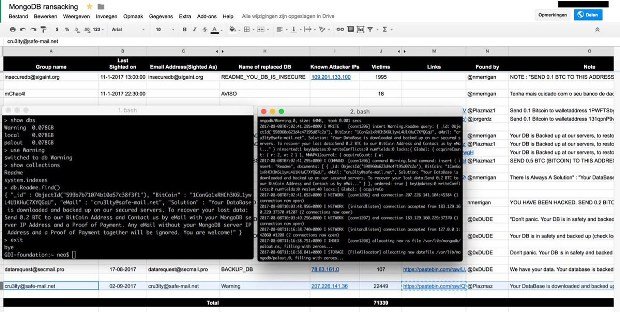
Massive Wave of MongoDB Ransom Attacks Makes 26,000 New Victims
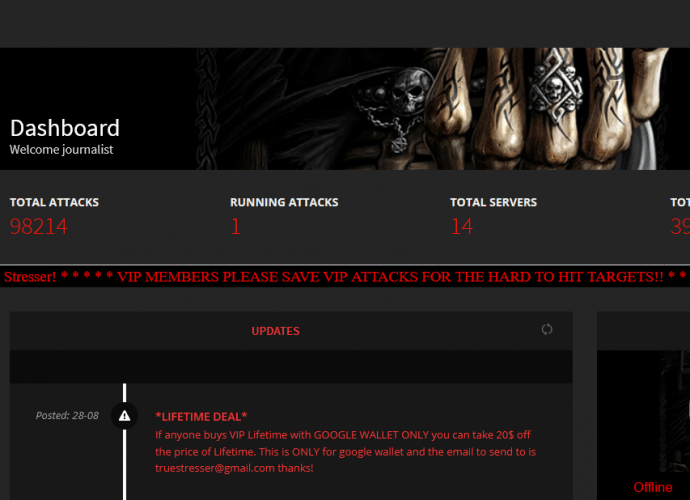
Ransom attacks on MongoDB databases rekindled last week and over the weekend with the emergence of three new groups that hijacked over 26,000 servers, with one group hijacking 22,000. TheRead More →