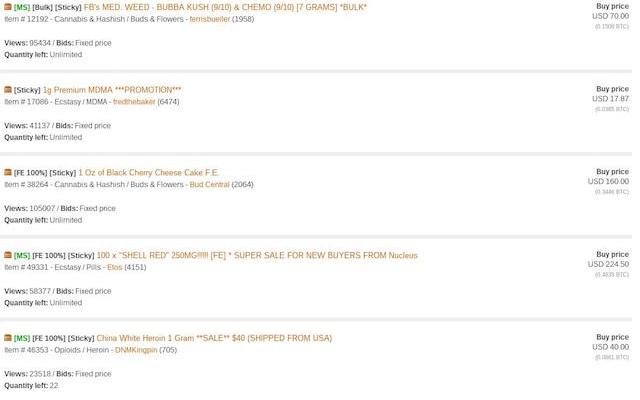
AlphaBay Market, one of the largest Dark Web marketplaces is down. Is it an Exit-Scam?
The AlphaBay Market went down Tuesday night without any explanation, many users that have purchased products on the marketplace fear the Exit-Scam. The news is shocking, the AlphaBay Market, one ofRead More →