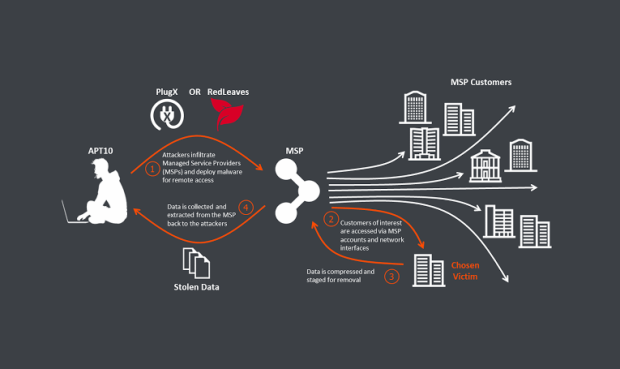
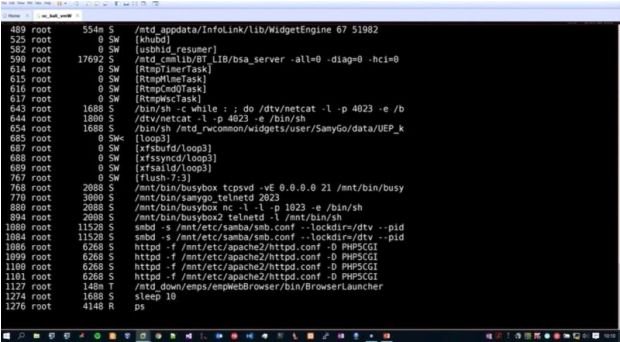
Chinese Group Is Hacking Cloud Providers to Reach Into Secure Enterprise Networks
A cyber-espionage group that first surfaced in 2009 is using a novel tactic into hacking its targets by first breaching one of its cloud service providers, and then reaching insideRead More →