Analyzing a variant of the GM Bot Android malware
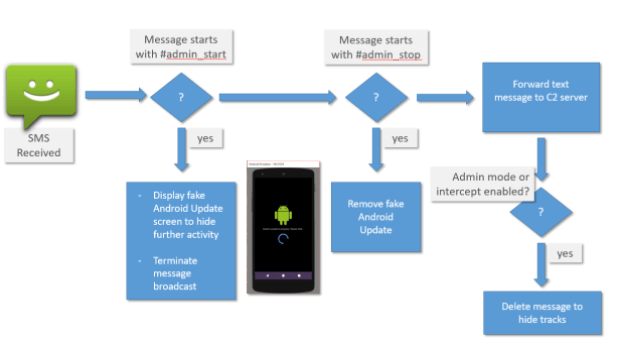
My friends at CyberBlog decided to analyze the GM Bot Android Malware as exercise aiming to receive feedback sand suggestions from the security community. The sample explored is confirmed as a variantRead More →