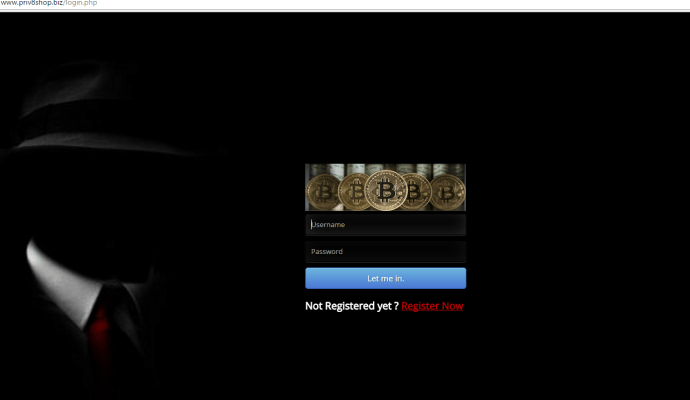
MongoDB Databases Held Up for Ransom by Mysterious Attacker
An attacker going by the name of Harak1r1 is hijacking unprotected MongoDB databases, stealing their content, and asking for a Bitcoin ransom to return the data. These attacks have beenRead More →