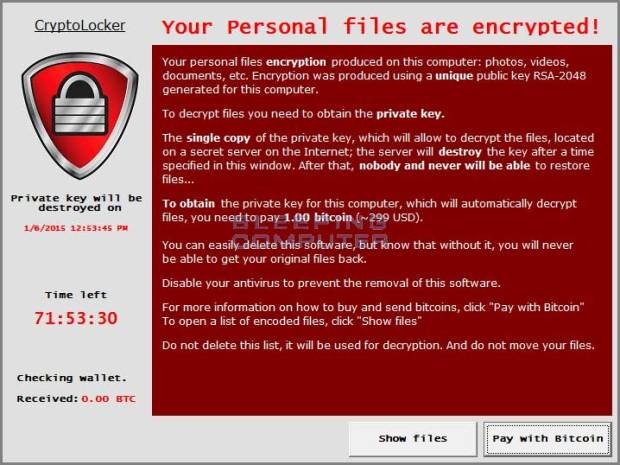
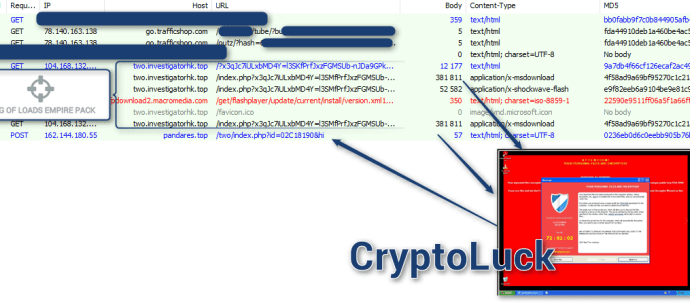
RIG-E Exploit Kit now distributing New CHIP Ransomware
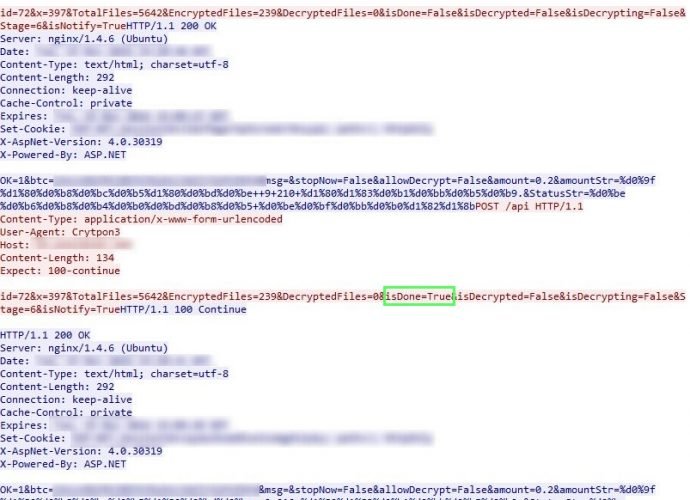
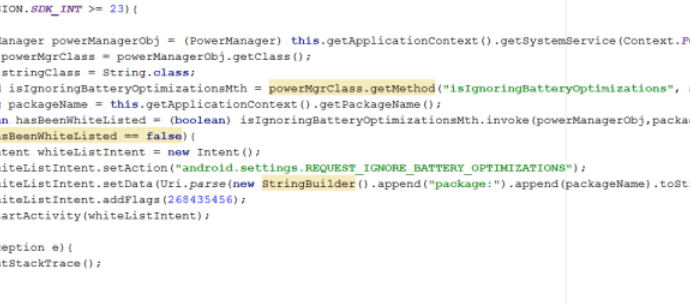
Brad Duncan, a security researcher for Rackspace, is well known for monitoring exploit kit activity and the payloads that are being distributed by them. In an article posted yesterday, BradRead More →