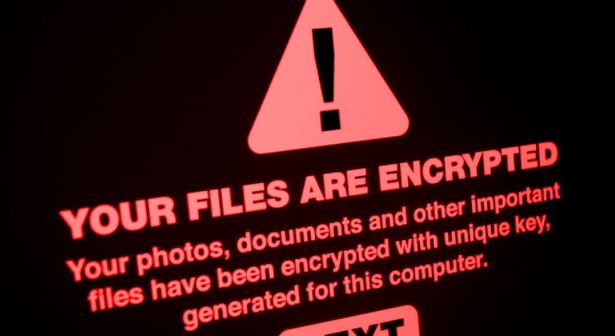
Critical vulnerability with 9/10 score in VMware products allows hackers to take full control of their networks
In its latest alert, the Cybersecurity and Infrastructure Security Agency (CISA) invites VMware administrators to update their deployments to address a critical vulnerability in Workspace ONE UEM. According to theRead More →