Azure DDoS Protection service was unable to protect Microsoft, how it will protect clients?
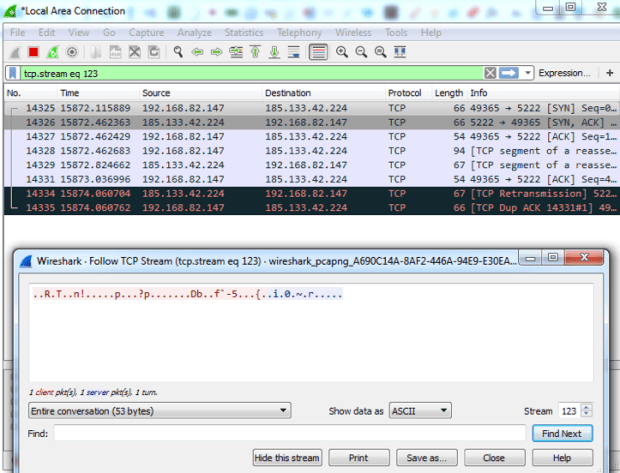
In recent weeks, a hacker collective calling itself Anonymous Sudan has been responsible for launching distributed denial of service attacks (DDoS) on a number of Microsoft services, including Outlook, OneDrive,Read More →