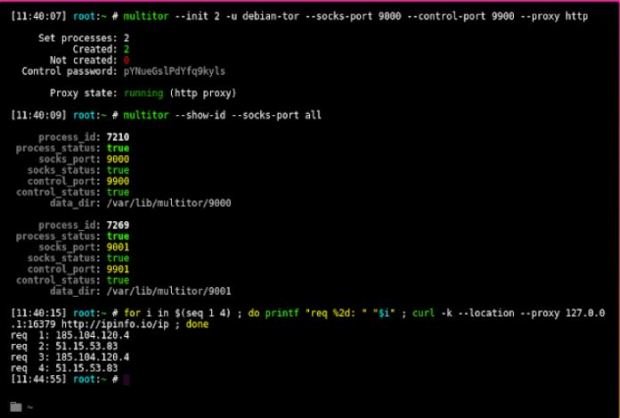
Bank of Montreal was hacked, one of the most important banks in Canada
Lately we have seen many attacks on banks, this time the malicious actors have turned to two Canadian banks. According to information security experts, hackers have stolen financial information fromRead More →