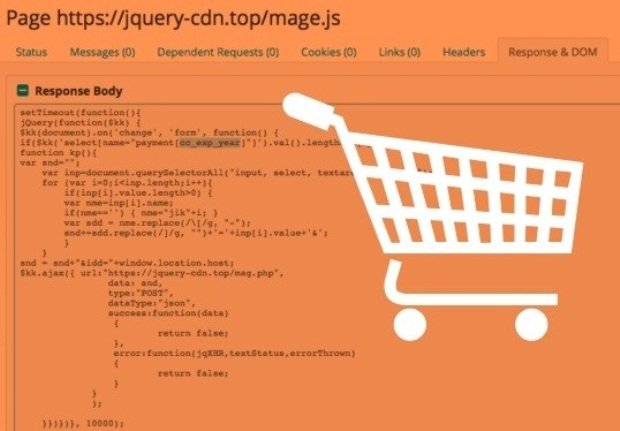
Over 100 Online Stores Targeted with New Magecart Malware
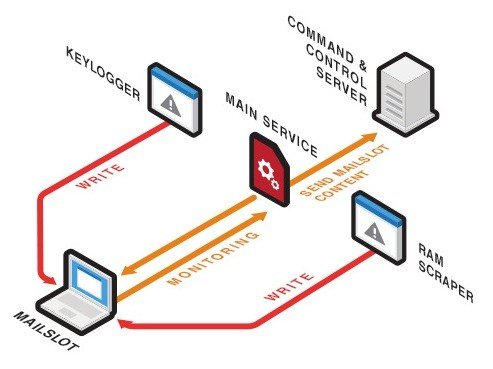
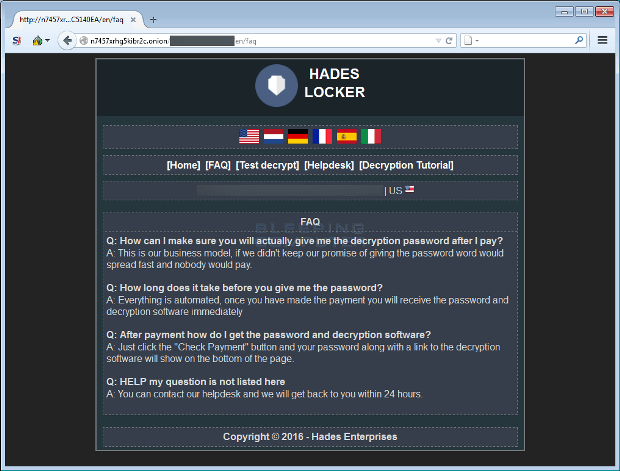
Magecart targets Magento, OpenCart and the Powerfront CMS. Over 100 online stores have been compromised with a new type of web malware called Magecart that secretly logs data entered onRead More →