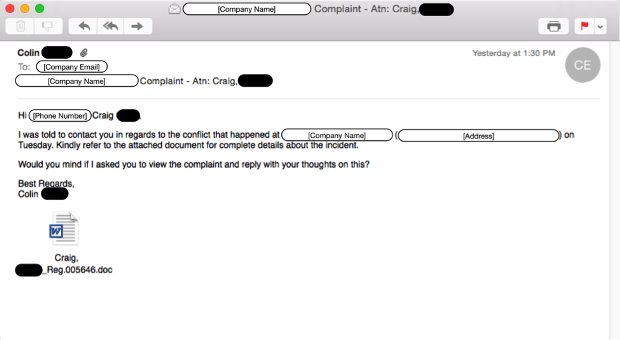
AceDeceiver: First iOS Trojan Exploiting Apple DRM Design Flaws to Infect Any iOS Device
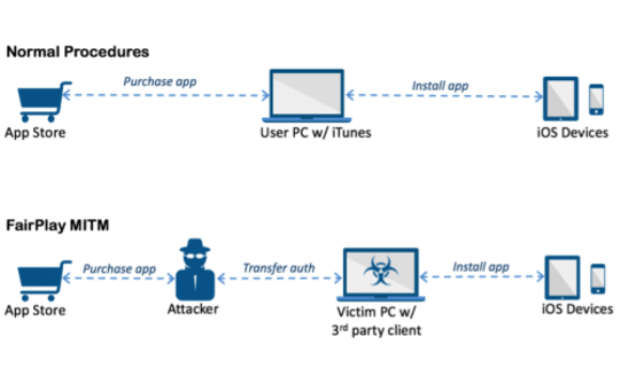
We’ve discovered a new family of iOS malware that successfully infected non-jailbroken devices we’ve named “AceDeceiver”. What makes AceDeceiver different from previous iOS malware is that instead of abusing enterprise certificatesRead More →