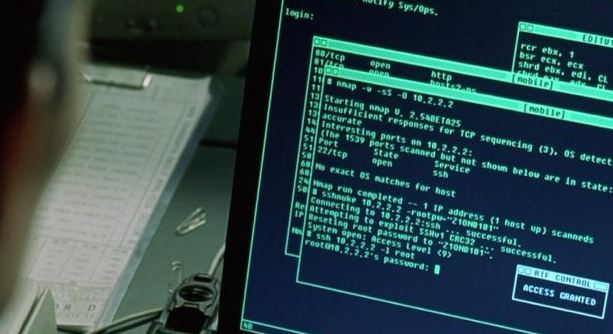
Government agency data breach exposes sensitive information of millions of people
Through a security report, the US Agency for Global Media (USAGM) revealed that it was the victim of a data breach that would have exposed the confidential information of formerRead More →