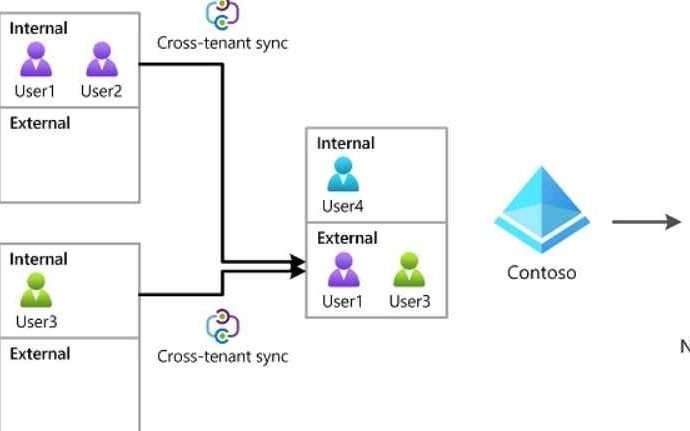
New Azure AD Cross-Tenant Synchronisation (CTS) Attack allows hacking tenants laterally
Attackers are still focusing their attention on Microsoft identities in the hopes of breaking into linked Microsoft apps and federated SaaS applications. In addition, attackers continue to advance their attacksRead More →