MongoDB improves security amid new wave of ransom-attacks
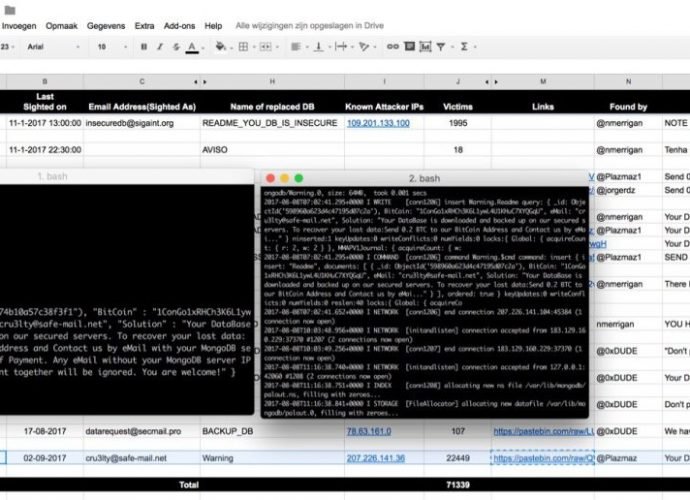
MongoDB company implements new data security features in response to the recent wave of ransom attacks that hit installations worldwide. You have to admit that the bad actors are very goodRead More →