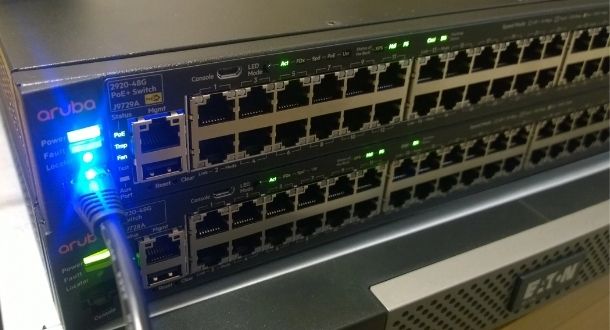
Critical vulnerability in Cisco Enterprise NFV Infrastructure Software (NFVIS) would allow easy root access to affected servers
In its latest security advisory Cisco announced the fix of several flaws in its NFV Infrastructure Software (NFVIS), a network virtualization solution for virtual network function (VNF) management. Two ofRead More →